Create a culture of security awareness and alertness with our managed phishing simulation service
-
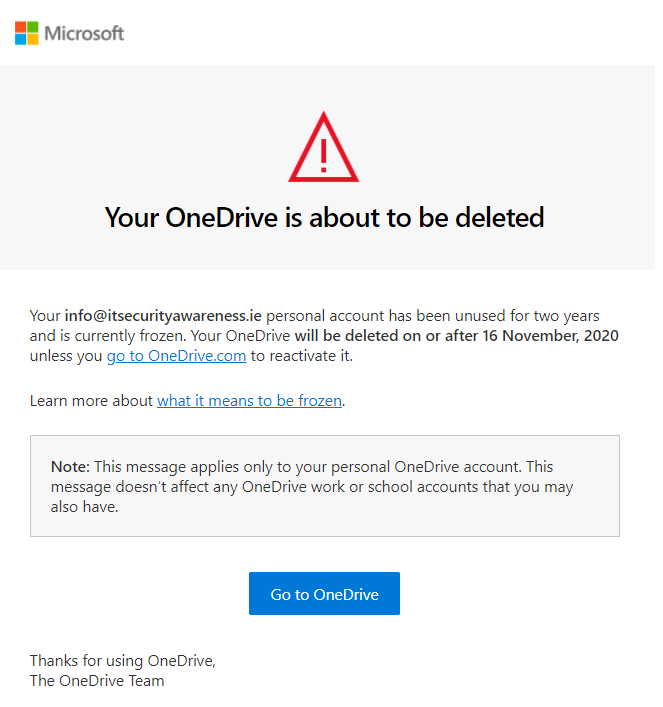
Realistic phishing simulations based on real-life attacks on Irish users.
-
Campaigns are typically delivered bi-monthly or monthly.
-
Our simulated phishing campaigns can be tailored to employees according to department or job role. For example, your finance department will receive finance themed emails while the sales department will receive sales themed ones.
-
Full and detailed reporting enabling you to flag your most susceptible users and see improvements over time.




Our reporting dashboard. Our reports can also be delivered in Excel, PDF or CSV format.



